Delivery options
OTP (SMS, mobile app) default delivery options work perfectly for most users; ESA can also accommodate custom delivery options.
In ESA Web Console, click Settings ![]() > Delivery Options.
> Delivery Options.
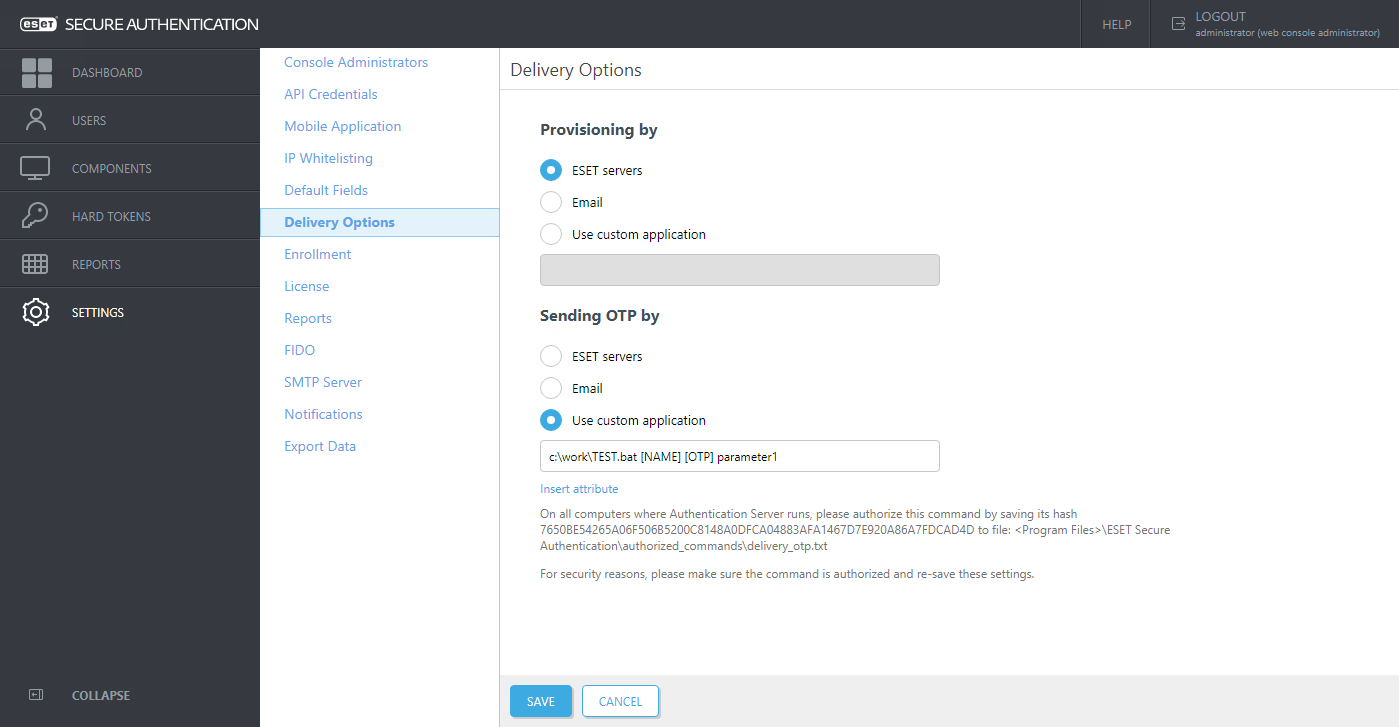
Select Email, or specify the path to your custom script by which you want to handle provisioning or delivery of OTP. Click Insert attribute to view a list of available parameters you can pass to your custom script. For example, to deliver the OTP, you must use the [OTP] parameter. You can also specify a custom string to be passed to your script (see parameter1 in the screenshot above).
Authorize commands
In ESET Secure Authentication On-Prem version 3.0.21 and later, the Use custom application option requires command authorization.
1.Create an "authorized_command" folder in the folder displayed under the command field. In our example, C:\Program Files\ESET Secure Authentication On-Prem\.
2.Based on the instructions under the command line field, create "delivery_provisioning.txt" or "delivery_opt.txt" in the "authorized_command" folder and save the provided hash in the folder.
3.Click Save.
Use email as the default delivery/provisioning option
To deliver OTP and/or provisioning information via email, define the details of a working SMTP server first:
1.In the ESA Web Console, click Settings > SMTP Server and fill in the required details.
a.If SSL/TLS is used, the SMTP's SSL certificate must be trusted by the server hosting the Authentication Server.
2.Use the Send test email to test the configuration. If an email is delivered to the provided email address, the configuration is correct.
3.In Settings ![]() > Delivery Options, select Email, click Save.
> Delivery Options, select Email, click Save.
4.Enable SMS-based OTPs per user:
a.Click Users.
b.Click a user, enable SMS-based OTPs, click Save.
5.If self-enrollment is enabled, ensure SMS-based OTPs is enabled at Settings > Enrollment > Default authentication types.
Security of authentication options ESA offers a wide range of 2FA methods that fit the varying preferences of our customers. The most secure and highly usable is Mobile Application Push (Push authentication). Still highly reliable, but in some situations, less convenient are: Mobile Application OTP, Hard Token, and FIDO. SMS-based OTPs, thus still available, are not considered the most secure mainly due to the underlying security used in the SMS delivery systems. When choosing the delivery of OTP by email, there might be usage schemas having weaker security. |
Sample scenario available in Active Directory Integration deployment type - Delivering OTP via custom email solution (application)
Prerequisite
•Know the SMTP details of the email gateway you want to use for sending the email message containing the OTP.
•Have a custom script for sending email messages.
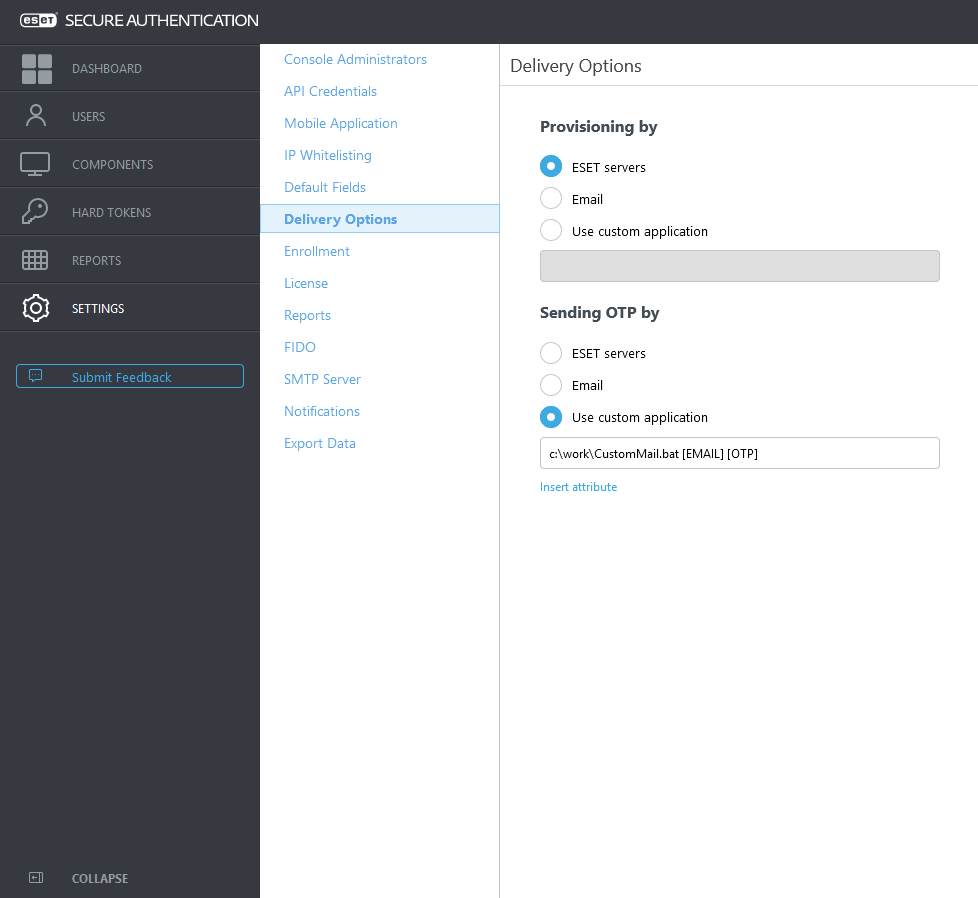
•Have a custom .BAT script you define the path to it in the ESA Web Console as shown in the screenshot above, while this .BAT script is going to call your custom script that is supposed to send the email message.
•Every 2FA-enabled user who receives OTP passwords via email must have their email address defined in the General tab's Email field when viewing their details through the Active Directory Users and Computers management interface.
SMTP details In the sample python script above the smtpserver:port, username and password are supposed to be replaced with the corresponding SMTP details. |
Sample .BAT script for calling the sendmail.py script while passing the essential parameters to it - we name the file as CustomMail.bat
c:\Python\python.EXE c:\work\sendmail.py %1 %2
Prerequisite This sample scenario assumes the python library is installed in your main computer where the ESA Authentication Server component is installed, and you know the path to the python.exe file. |
In the Sending OTP by field, define the path leading to CustomMail.bat script, select the essential parameters such as [E-mail-Addresses] and [OTP] and then click Save
Provisioning (delivery of the mobile application) can be customized the same way using the [PHONE] and [URL] parameters.
Email vs SMS delivery Compared to SMS delivery (or usage of provisioned mobile application), email as the means of OTP distribution is slightly less secure because the email can be read on any device the user possesses. This method does not confirm that the intended recipient owns the registered phone (phone number). |