Potentially unwanted applications
Grayware or Potentially unwanted application (PUA) is a broad software category whose intent is not as unequivocally malicious as with other types of malware, such as viruses or trojans. It may, however, install additional unwanted software, change the behavior of the digital device, or perform activities not approved or expected by the user.
Categories that may be considered grayware include advertising display software, download wrappers, various browser toolbars, software with misleading behavior, bundleware, trackware, proxyware (internet-sharing applications), crypto-miners, registry cleaners (Windows operating systems only) or any other borderline software, or software that uses illicit or at least unethical business practices (despite appearing legitimate) and might be deemed undesirable by an end user who became aware of what the software would do if allowed to install.
A Potentially Unsafe Application is legitimate (possibly commercial) software that attackers might misuse.
In some situations, a user may feel that the benefits of a potentially unwanted application outweigh the risks. For this reason, ESET assigns such applications a lower-risk category compared to other types of malicious software, such as trojans or worms.
Further information about this topic can be found in this ESET Knowledgebase article.
Also in this chapter:
Software wrappers
A software wrapper is a special type of application modification that is used by some file-hosting websites. It is a third-party tool that installs the program you intended to download but adds additional software, such as toolbars or adware. The additional software may change your web browser’s home page and search settings. Also, file-hosting websites often do not notify the software vendor or download recipient that modifications are made, and often hide options to opt out. For these reasons, ESET classifies software wrappers as potentially unwanted applications that allow users to accept the download.
Registry cleaners
Registry cleaners suggest that the Windows registry database requires regular maintenance or cleaning. Using a registry cleaner might introduce some risks to your computer system. Additionally, some registry cleaners make unqualified, unverifiable, or otherwise unsupportable claims about their benefits or generate misleading reports about a computer system based on "free scan" results. These misleading claims and reports seek to persuade you to purchase a full version or subscription, usually without allowing you to evaluate the registry cleaner before payment. For these reasons, ESET classifies such programs as PUA and allows you to allow or block them.
Detections in ESET products
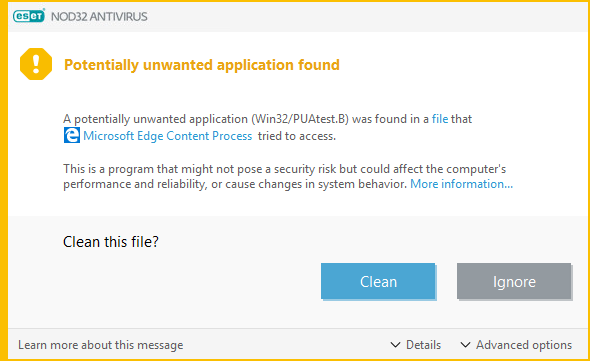
Warning—Potentially unwanted application found
When a potentially unwanted application is detected, you can decide which action to take:
•Clean/Disconnect—This option ends the action and prevents the PUA from entering your system.
You will see the Disconnect option for PUA notifications during download from a website and the Clean option for notifications for a file on disk.
•Ignore—This option allows a PUA to enter your system.
Actions available under Advanced options might not be available by default, depending on ESET product's remediation strategy:
•Exclude from detection—To allow the detected file that is already on the computer to run in the future without interruption, click Advanced options, select the check box next to Exclude from detection and click Ignore.
•Exclude signature from detection—To allow all files identified by a specific detection name (signature) to run on your computer in the future without interruption (from existing files or web downloads), click Advanced options, select the check box next to Exclude signature from detection and click Ignore. If additional detection windows with an identical detection name are displayed immediately afterward, click Ignore to close them (any additional windows are related to a detection that occurred before you excluded the signature from detection).
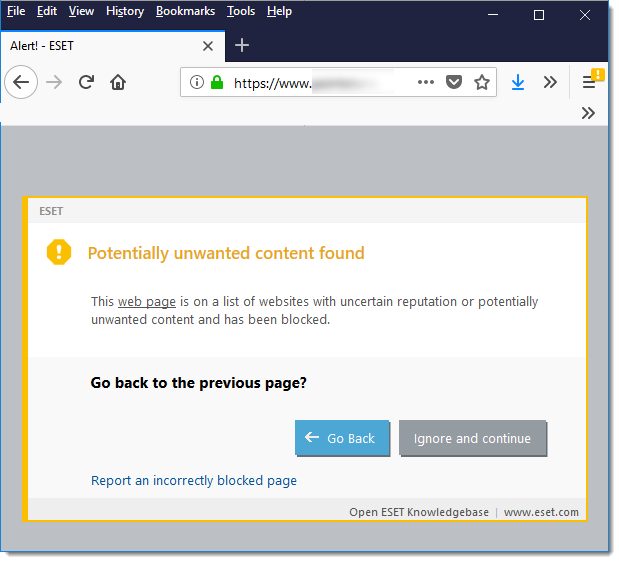
Potentially unwanted content found
If PUA detection is enabled in your ESET product, websites that have a reputation for promoting PUAs or that have a reputation for misleading users into performing actions that might have negative implications on their system or browsing experience will be blocked as potentially unwanted content. You can be notified that a website you are attempting to visit is categorized as potentially unwanted content. Click Go Back to navigate away from the blocked web page, or, if you trust the website content, add it first to the List of allowed addresses to continue.
ESET product settings
While installing your ESET product, you can decide whether to enable the detection of potentially unwanted applications, as shown below:
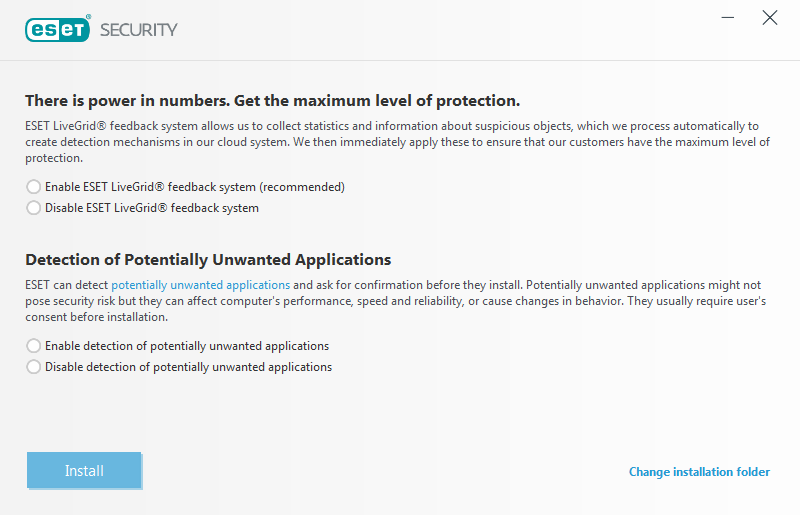
Warning Potentially unwanted applications may install adware and toolbars or contain other unwanted and unsafe program features. |
Users of ESET software can turn on or off detection of these types of applications, as well as manage exclusions for specific executables.
To enable or disable the overall detection, follow these instructions:
2.Press the F5 key to access Advanced setup.
3.Click Protections.
4.Select settings next to Potentially unwanted applications according to your preferences.
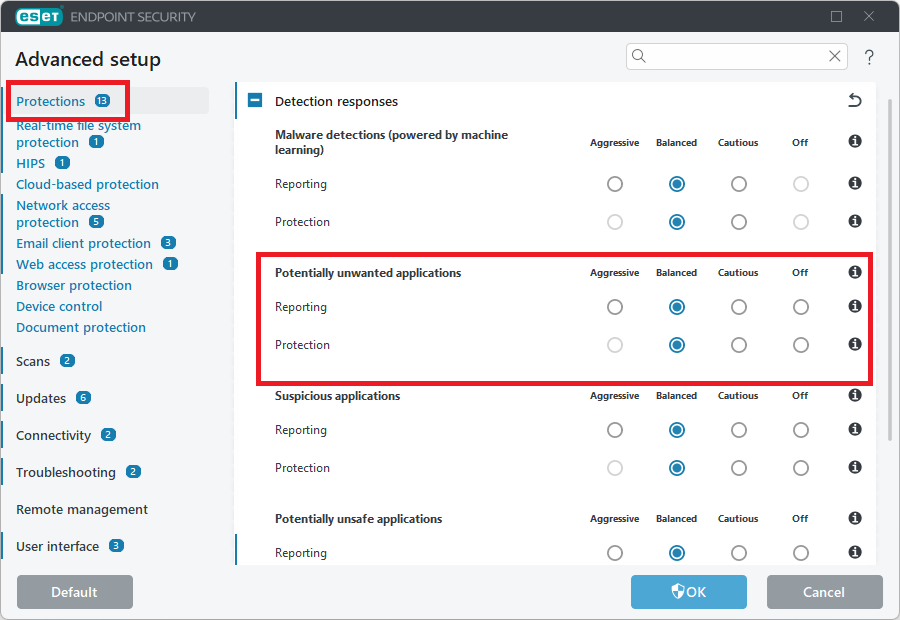
5.Click OK to save your changes.
Illustrated instructions See our ESET Knowledgebase article to scan and remove Potentially Unwanted Applications (PUAs) in ESET Windows home products. For more detailed instructions on how to configure products to detect or ignore PUAs, visit ESET Knowledgebase articles: •ESET Windows home products (ESET Internet Security) •ESET Cyber Security for macOS •ESET Endpoint Security / ESET Endpoint Antivirus for Windows |