Detection engine guards against malicious system attacks by scanning files, emails and network communication. If an object classified as malware is detected, remediation will start. Detection engine can eliminate it by first blocking it and then taking action such as cleaning, deleting or moving to quarantine.
Real-time & Machine learning protection
Advanced machine learning is now a part of the detection engine as an advanced layer of protection, which improves detection based on machine learning. Read more about this type of protection in the glossary. You can configure Reporting and Protection levels of the following categories:
Malware
A computer virus is a malicious code prepended or appended to existing files on your computer. However, the term "virus" is often misused. "Malware" (malicious software) is a more accurate term. Malware detection is performed by the detection engine module combined with the Machine learning component. Read more about these types of applications in the glossary.
Potentially unwanted applications (PUAs)
A Potentially unwanted application is a software with an intent not unequivocally malicious, however; it may install additional unwanted software, change the behavior of the digital device, perform activities not approved or expected by the user or has unclear objectives.
This category includes advertising display software, download wrappers, various browser toolbars, software with misleading behavior, bundleware, trackware, etc. Read more about these types of applications in the glossary.
Potentially suspicious applications
Is a software compressed with packers or protectors frequently used to deter reverse engineering or to obfuscate the content of the executable (for example, to hide the presence of malware) by proprietary methods of compression and/or encryption.
This category includes: all unknown applications that are compressed with a packer or protector frequently used to compress malware.
Potentially unsafe applications
This classification is given for commercial, legitimate software that might be misused for malicious purposes. An unsafe application refers to legitimate commercial software that has the potential to be misused for malicious purposes.
This category includes: cracking tools, license key generators, hacking tools, remote access or control tools, password-cracking applications and keyloggers (programs that record each keystroke typed by a user). This option is disabled by default.
Read more about these types of applications in the glossary.
Read the following before modifying a threshold (or level) for category Reporting or Protection:
Reporting is performed by the detection engine and machine learning component. You can set the reporting threshold to better suit your environment and needs. There is not a single correct configuration. Therefore, we recommend that you monitor the behavior within your environment and decide whether a different Reporting setting is more suitable.
Reporting does not take action with objects, it passes information to a respective protection layer, and the protection layer takes action accordingly.
Aggressive
|
Reporting configured to maximum sensitivity. More detections are reported. While the Aggressive setting may appear to be the safest, it can often be too sensitive, which might even be counterproductive.
|

|
The aggressive setting may falsely identify objects as malicious, and action will be taken with such objects (depending on Protection settings).
|
|
Balanced
|
This setting is an optimal balance between performance and accuracy of detection rates and the number of falsely reported objects.
|
Cautious
|
Reporting configured to minimize falsely identified objects while maintaining a sufficient level of protection. Objects are reported only when the probability is evident and matches malicious behavior.
|
Off
|
Reporting is not active. Detections are not found, reported or cleaned.
|

|
Malware reporting cannot be deactivated; therefore, the Off setting is not available for Malware.
|
|
If you want to Revert settings in this section to their default values, click the "U-turn" arrow next to the section header. Any changes you have made in this section will be lost.
|
Reporting
Performed by detection engine and the machine learning component. Reporting does not take an action with objects (this is done by respective protection layer).
Protection
Configure parameters in Mail transport protection to affect what action is taken with reported objects. Also, you can configure a custom rule:
|

|
Core installation example:
Objective: Quarantine messages that contain malware or attachment that is password protected, encrypted or damaged
Create the following rule for Mail transport protection:
Condition
Type: Antivirus scan result
Operation: is
Parameter: Infected – not cleaned
Action
Type: Quarantine message
|
If you want to Revert settings in this section to their default values, click the "U-turn" arrow next the to section header. Any changes you have made in this section will be lost.
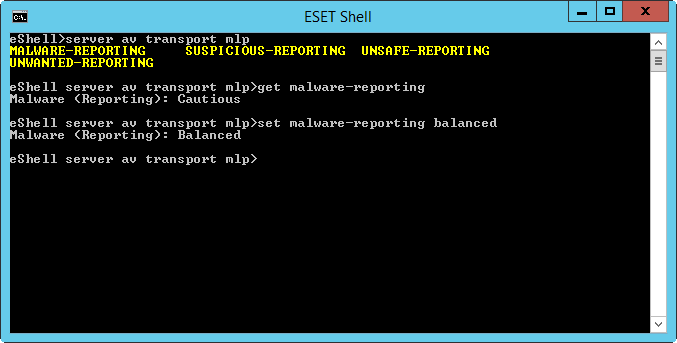
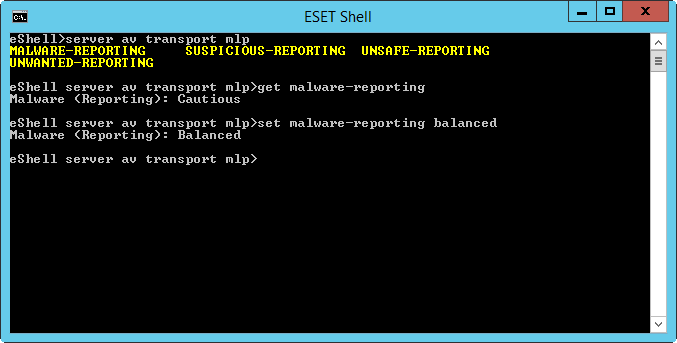
Configure Machine learning protection using eShell. The Context name in eShell is MLP. Open eShell in interactive mode and navigate to MLP:
server av transport mlp
See what is the current reporting setting for Suspicious applications:
get suspicious-reporting
If you want less strict reporting, change the setting to Cautious:
set suspicious-reporting cautious
|
Reporting
Performed by detection engine and the machine learning component. Reporting does not take an action with objects (this is done by respective protection layer).
Protection
Configure parameters in Mailbox database protection to affect what action is taken with reported objects.
If you want to Revert settings in this section to their default values, click the "U-turn" arrow next the to section header. Any changes you have made in this section will be lost.
Configure Machine learning protection using eShell. The Context name in eShell is MLP. Open eShell in interactive mode and navigate to MLP:
server av database mlp
See what is the current reporting setting for Suspicious applications:
get suspicious-reporting
If you want less strict reporting, change the setting to Cautious:
set suspicious-reporting cautious
|
Reporting
Performed by detection engine and the machine learning component. Reporting does not take an action with objects (this is done by respective protection layer).
Protection
Configure parameters in On-demand mailbox database scan to affect what action is taken with reported objects.
If you want to Revert settings in this section to their default values, click the "U-turn" arrow next the to section header. Any changes you have made in this section will be lost.
Configure Machine learning protection using eShell. The Context name in eShell is MLP. Open eShell in interactive mode and navigate to MLP:
server av on-demand mlp
See what is the current reporting setting for Suspicious applications:
get suspicious-reporting
If you want less strict reporting, change the setting to Cautious:
set suspicious-reporting cautious
|