Audit Log
The Audit log tracks various event types that occur. There are three severity types that can be associated with an event: Information (blue), Warning (yellow) and Error (red). Each log entry shows the action that occurred, a description of the action, the severity level, the time of occurrence, the username and the IP Address where the action occurred.
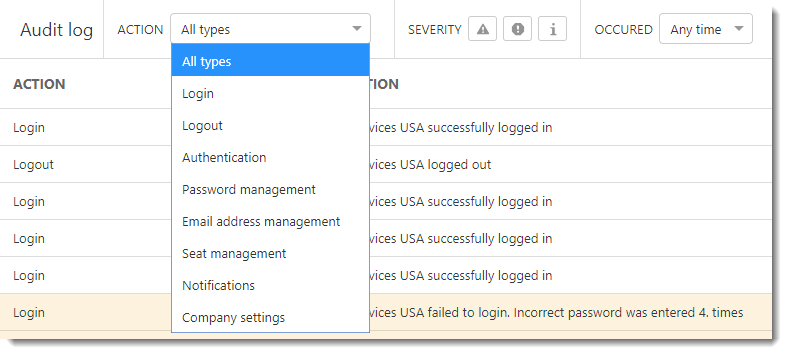
Use the Action drop-down menu to filter log entries by type. You can also filter by the event severity or time of occurrence.
Logs are created for the following event types:
•Login/ Logout—Successful user account login/logout and failed logins
•Authentication—Successful authentication using username and password or OTP, incorrect authentication attempts, 2FA enabled, configured or disabled, and backup code used for authentication
•Password management—Requests for forgotten passwords, password changes, used invalid/expired passwords or password tokens
•Email address management—User requests for email address changes, email address confirmations/cancellations and changes, invalid or expired tokens, etc.
•User management—New user account creation/confirmation, account details changes, account deletions, resent activation links, etc.
•License management—Newly added licenses, license registrations, license registration edits, license removal from company, other license file changes
•Business account management—New business account registration, registration confirmation,and expired account registration tokens
•Company management—Company details changes, new access rights added, new ECA instance created, suspended, deleted, etc.
•Site management—New site created, site removed from company, details edited, new licenses added, removed, units updated
•Unit management—User activates a seat using a license associated with an EBA account, seat deactivated, disassociated, renamed, or moved to another site
•Alerts—Marked as resolved or not resolved
•Settings—Business account settings are changed
The Audit log menu is only available to the root user of the company, not to additional users. |
Impersonation logs
Distributors and MSP Managers can impersonate subordinate accounts. Any activity of the impersonated user is logged in the Audit Log. Click the User Impersonation checkbox in the header of the Audit Log screen, to filter out impersonation logs.
![]()