Protections
Protections guard against malicious system attacks by controlling file, email and internet communications. For example, remediation will start if an object classified as malware is detected. Protections can eliminate it by blocking it and then cleaning, deleting or moving it to quarantine.
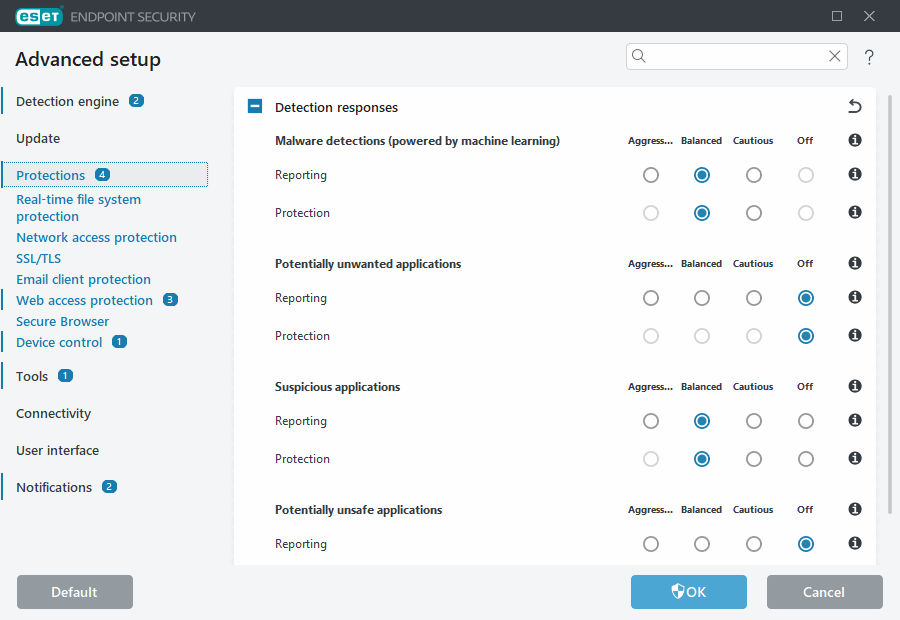
To configure protections in detail, open Advanced setup > Protections.
Changes to Protections should only be made by an experienced user. Incorrect configuration of settings can lead to a decreased level of protection. |
In this section:
Detection responses
Detection responses enable you to configure reporting and protection levels for the following categories:
- Malware detections (powered by machine learning)—A computer virus is a piece of malicious code that is prepended or appended to existing files on your computer. However, the term “virus” is often misused. "Malware” (malicious software) is a more accurate term. Malware detection is performed by the detection engine module combined with the machine learning component. Read more about these types of applications in the Glossary.
- Potentially unwanted applications—Grayware or potentially unwanted applications (PUAs) is a broad category of software, whose intent is not as unequivocally malicious as other types of malware, such as viruses or trojan horses. However, it could install additional unwanted software, change the behavior of the digital device, or perform activities not approved or expected by the user. Read more about these types of applications in the Glossary.
- Suspicious applications—Includes programs compressed with packers or protectors. These types of protectors are often exploited by malware authors to evade detection.
- Potentially unsafe applications—Refers to legitimate commercial software that has the potential to be misused for malicious purposes. Examples of potentially unsafe applications (PUAs) include remote access tools, password-cracking applications, and keyloggers (programs recording each keystroke typed by a user). Read more about these types of applications in the Glossary.
Improved protection Advanced machine learning is now a part of the protections as an advanced layer of protection which improves detection based on machine learning. Read more about this type of protection in the Glossary. |
Reporting setup
When a detection occurs (e.g., a threat is found and classified as malware), information is recorded to the Detections log, and Desktop notifications occur if configured in ESET Endpoint Security.
A reporting threshold is configured for each category (referred to as "CATEGORY"):
- Malware detections
- Potentially unwanted applications
- Potentially unsafe
- Suspicious applications
Reporting is performed with the detection engine, including the machine learning component. You can set a higher reporting threshold than the current protection threshold. These reporting settings do not influence blocking, cleaning or deleting objects.
Read the following before modifying a threshold (or level) for CATEGORY reporting:
Threshold |
Explanation |
|---|---|
Aggressive |
CATEGORY reporting configured to maximum sensitivity. More detections are reported. The Aggressive setting can falsely identify objects as CATEGORY. |
Balanced |
CATEGORY reporting configured as balanced. This setting is optimized to balance the performance and accuracy of detection rates and the number of falsely reported objects. |
Cautious |
CATEGORY reporting configured to minimize falsely identified objects while maintaining a sufficient level of protection. Objects are reported only when the probability is evident and matches CATEGORY behavior. |
Off |
Reporting for CATEGORY is not active, and detections of this type are not found, reported or cleaned. As a result, this setting disables protection from this detection type. |
Availability of ESET Endpoint Security protection modules
Determine product version, program module versions and build dates
Keynotes
Several keynotes when setting up an appropriate threshold for your environment:
- The Balanced threshold is recommended for most of the setups.
- The Cautious threshold is recommended for environments where the priority focuses on minimizing false identified objects by security software.
- The higher reporting threshold, the higher detection rate but a higher chance of falsely identified objects.
- From the real-world perspective, there is no guaranty of a 100% detection rate as well as a 0% chance to avoid incorrect categorization of clean objects as malware.
- Keep ESET Endpoint Security and its modules up-to-date to maximize the balance between performance and accuracy of detection rates and the number of falsely reported objects.
Protection setup
If an object classified as CATEGORY is reported, the program blocks the object and then cleans, deletes or moves it to Quarantine.
Read the following before modifying a threshold (or level) for CATEGORY protection:
Threshold |
Explanation |
|---|---|
Aggressive |
Reported aggressive (or lower) level detections are blocked, and automatic remediation (i.e., cleaning) is started. This setting is recommended when all endpoints have been scanned with aggressive settings and falsely reported objects have been added to detection exclusions. |
Balanced |
Reported balanced (or lower) level detections are blocked, and automatic remediation (i.e., cleaning) is started. |
Cautious |
Reported cautious level detections are blocked, and automatic remediation (i.e., cleaning) is started. |
Off |
Useful to identify and exclude falsely reported objects. |
Best practices
UNMANAGED (Individual client workstation)
Keep the default recommended values as is.
MANAGED ENVIRONMENT
These settings are usually applied to workstations via a policy.
1. Initial phase
This phase might take up to a week.
- Set up all Reporting thresholds to Balanced.
NOTE: If needed, set up to Aggressive. - Set up or keep Protection for malware as Balanced.
- Set up Protection for other CATEGORIES to Cautious.
NOTE: It is not recommended to set up the Protection threshold to Aggressive in this phase because all found detections would be remediated, including the falsely identified ones. - Identify falsely identified objects from Detections log and add them to Detection exclusions first.
2. Transition phase
- Implement the "Production phase" to some of the workstations as a test (not for all workstations on the network).
3. Production phase
- Set up all Protection thresholds to Balanced.
- When managed remotely, use an appropriate antivirus pre-defined policy for ESET Endpoint Security.
- Aggressive protection threshold can be set if the highest detection rates are required and falsely identified objects are accepted.
- Check Detection log or ESET PROTECT On-Prem reports for possible missing detections.
