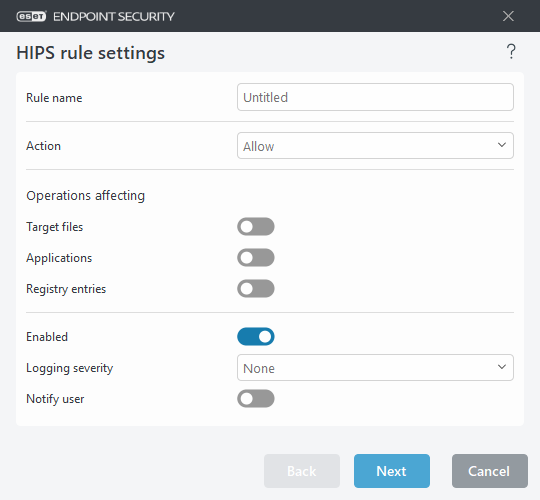
HIPS rule settings
See HIPS rule management as first.
Rule name—User-defined or automatically chosen rule name.
Action—Specifies an action – Allow, Block or Ask – that should be performed if conditions are met.
Operations affecting—You must select the type of operation for which the rule will be applied. The rule will be used only for this type of operation and for the selected target.
Enabled—Disable this switch if you want to keep the rule in the list but not apply it.
Logging severity—If you activate this option, information about this rule will be written to the HIPS log.
Notify user—A notification appears in the lower-right corner if an event is triggered.
The rule consists of parts that describe the conditions triggering this rule:
Source applications—The rule will be used only if the event is triggered by this application(s). Select Specific applications from drop-down menu and click Add to add new files or you can select All applications from the drop-down menu to add all applications.
Target files—The rule will be used only if the operation is related to this target. Select Specific files from drop-down menu and click Add to add new files or folders or you can select All files from the drop-down menu to add all files.
Applications—The rule will be used only if the operation is related to this target. Select Specific applications from the drop-down menu and click Add to add new files or folders or you can select All applications from the drop-down menu to add all applications.
Registry entries—The rule will be used only if the operation is related to this target. Select Specific entries from the drop-down menu and click Add to add new files or folders, or you can select All entries from the drop-down menu to add all applications.
Some operations of specific rules pre-defined by HIPS cannot be blocked and are allowed by default. In addition, not all system operations are monitored by HIPS. HIPS monitors operations that may be considered unsafe. |
When specifying a path, C:\example affects actions with the folder itself, and C:\example*.* affects the files in the folder. |
Application operations
- Debug another application—Attaching a debugger to the process. While debugging an application, many details of its behavior can be viewed and modified and its data can be accessed.
- Intercept events from another application—The source application is attempting to catch events targeted at a specific application (for example a keylogger trying to capture browser events).
- Terminate/suspend another application—Suspending, resuming or terminating a process (can be accessed directly from Process Explorer or the Processes pane).
- Start new application—Starting of new applications or processes.
- Modify state of another application—The source application is attempting to write into the target applications' memory or run code on its behalf. This functionality may be useful to protect an essential application by configuring it as a target application in a rule blocking the use of this operation.
Registry operations
- Modify startup settings—Any changes in settings that define which applications will be run at Windows startup. These can be found, for example, by searching for the Run key in the Windows Registry.
- Delete from registry—Deleting a registry key or its value.
- Rename registry key—Renaming registry keys.
- Modify registry—Creating new values of registry keys, changing existing values, moving data in the database tree or setting user or group rights for registry keys.
Using wildcards in rules An asterisk in rules can only be used to substitute a specific key, e.g. “HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\*\Start”. Other ways of using wildcards are not supported. Creating rules targeting HKEY_CURRENT_USER key This key is just a link to the appropriate subkey of HKEY_USERS specific to the user identified by SID (secure identifier). To create a rule only for the current user, instead of using a path to HKEY_CURRENT_USER, use a path pointing to HKEY_USERS\%SID%. As SID you can use an asterisk to make the rule applicable for all users. |
If you create a very generic rule, the warning about this type of rule will be shown. |
In the following example, we will demonstrate how to restrict unwanted behavior of a specific application:
- Name the rule and select Block (or Ask if you prefer to choose later) from the Action drop-down menu.
- Enable the Notify user switch to display a notification any time that a rule is applied.
- Select at least one operation in the Operations affecting section for which the rule will be applied.
- Click Next.
- In the Source applications window, select Specific applications from the drop-down menu to apply your new rule to all applications attempting to perform any of the selected application operations on the applications you specified.
- Click Add and then ... to choose a path to a specific application and then press OK. Add more applications if you prefer.
For example: C:\Program Files (x86)\Untrusted application\application.exe - Select the Write to file operation.
- Select All files from the drop-down menu. This will block any attempts to write to any files by the selected application(s) from the previous step.
- Click Finish to save your new rule.