Profile targets
You can specify what will be scanned for infiltrations. Choose objects (memory, boot sectors and UEFI, drives, files and folders or network) from the tree structure that lists all available targets on your system. Click the gear icon in the top-left corner to access the Scan targets and Scan profile drop-down menus.
This scan profile selector applies to On-demand scan and Hyper-V scan. |
Operating memory |
Scans all processes and data currently used by operating memory. |
|---|---|
Boot sectors/UEFI |
Scans Boot sectors and UEFI for the presence of malware. Read more about the UEFI scanner in the glossary. |
WMI database |
Scans the whole Windows Management Instrumentation (WMI) database, all namespaces, all class instances, and all properties. Searches for references to infected files or malware embedded as data. |
System registry |
Scans the whole system registry, all keys, and subkeys. Searches for references to infected files or malware embedded as data. When cleaning the detections, the reference remains in the registry to make sure no important data will be lost. |
To quickly navigate to a scan target or add a target folder or file(s), enter the target directory in the blank field below the folder list.
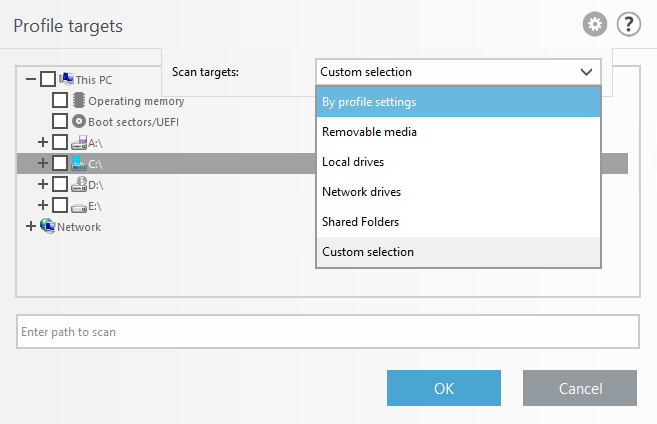
The Scan targets drop-down menu enables you to select pre-defined scan targets:
By profile settings |
Selects targets set in the selected scan profile. |
|---|---|
Removable media |
Selects diskettes, USB storage devices, CD/DVD. |
Local drives |
Selects all system hard drives. |
Network drives |
Selects all mapped network drives. |
Shared Folders |
Selects all folders on the local server that are shared. |
Custom selection |
Clears all selections. Ones cleared, you can make your custom selection. |
To quickly navigate to a scan target (file or folder) to include it for scanning, enter its path into the text field below the tree structure. The path entry is case sensitive.
The Scan profile drop-down menu enables you to select pre-defined scan profiles:
•Smart scan
•Context menu scan
•In-depth scan
•Computer scan
These scan profiles use different ThreatSense engine parameters.
Scan without cleaning
If you are only interested in scanning the system without additional cleaning actions, select Scan without cleaning. This is useful when you only want to obtain an overview whether there are infected items and get details about these infections, if there are any. You can choose from three cleaning levels by clicking Setup > ThreatSense parameters > Cleaning. Information about scanning is saved to a scan log.
Ignore exclusions
When you select Ignore exclusions, it lets you perform a scan while ignoring exclusions that otherwise apply.