Firewall rules
Firewall Rules represent a set of conditions used to meaningfully test all network connections and all actions assigned to these conditions. Using Firewall rules, you can define the action that is taken when different types of network connections are established.
Rules are evaluated from top to bottom and you can see their priority in the first column. The action of the first matching rule is used for each network connection being evaluated.
Connections can be divided into incoming and outgoing connections. Incoming connections are initiated by a remote device attempting to establish a connection with the local system. Outgoing connections work in the opposite way – the local system contacts a remote device.
If a new unknown communication is detected, you must carefully consider whether to allow or deny it. Unsolicited, unsecured or unknown connections pose a security risk to the system. If such a connection is established, we recommend that you pay attention to the remote device and the application attempting to connect to your computer. Many infiltrations try to obtain and send private data or download other malicious applications to host workstations. The Firewall enables you to detect and terminate such connections.
You can view and edit Firewall rules in Advanced setup > Protections > Network access protection > Firewall > Rules > Edit.
If you have many Firewall rules, you can use a filter to show only specific rules. To filter Firewall rules, click More filters above the Firewall rules list. You can filter the rules based on the following criteria:
- Origin
- Direction
- Action
- Availability
By default, the pre-defined Firewall rules are hidden. To display all pre-defined rules, disable the toggle next to Hide built-in (pre-defined) rules. You can disable these rules, but you cannot delete a pre-defined rule.
Click the search icon |
Columns
Priority—Rules are evaluated from top to bottom and you can see their priority in the first column.
Enabled—Shows if a rule is enabled or disabled; the corresponding check box must be selected to enable a rule.
Application—The application to which the rule applies.
Direction—Direction of communication (incoming/outgoing/both).
Action—Shows the status of communication (block/allow/ask).
Name—Name of the rule. The ESET Icon ![]() represents a pre-defined rule.
represents a pre-defined rule.
Times applied—Total number of times the rule has been applied.
Click the expand icon |
You can choose which columns are displayed by right-clicking on the table header. |
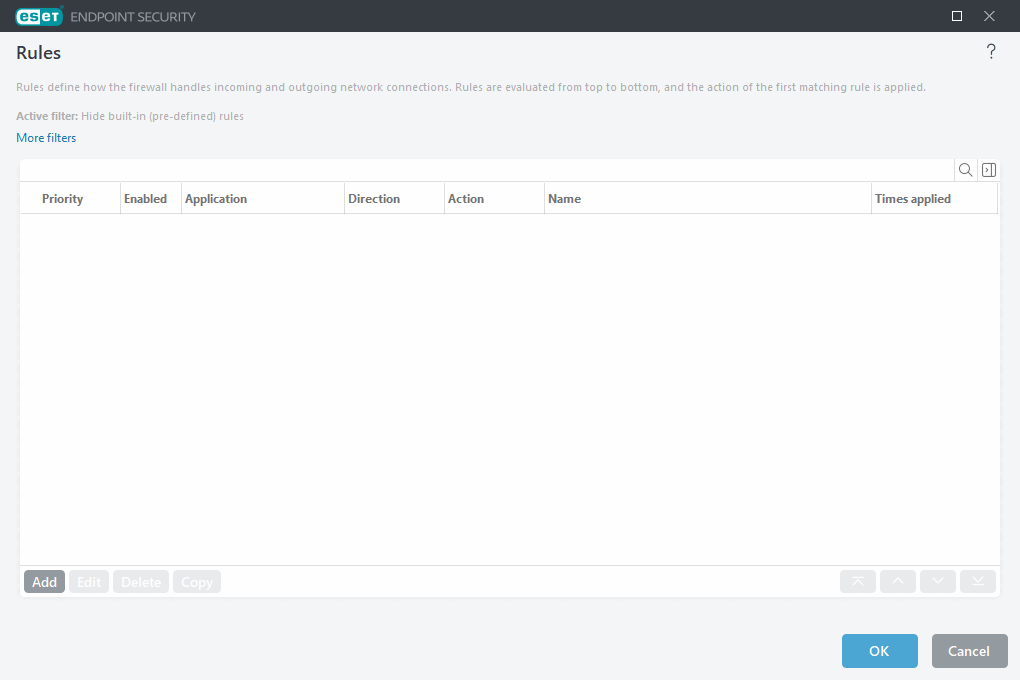
Control elements
Add—Create a new rule.
Edit—Edit an existing rule.
Delete—Remove an existing rule.
Copy—Create a copy of a selected rule.
![]() Top/Up/Down/Bottom—Enables you to adjust the priority level of rules (rules are executed from top to bottom).
Top/Up/Down/Bottom—Enables you to adjust the priority level of rules (rules are executed from top to bottom).
