Log files
The log files contain information about important program events and provide an overview of detected threats. Logging is essential for system analysis, threat detection and troubleshooting. Logging is actively performed in the background with no user interaction. Information is recorded based on current log verbosity settings. You can view text messages and logs directly from the ESET Cyber Security environment, and you can archive logs.
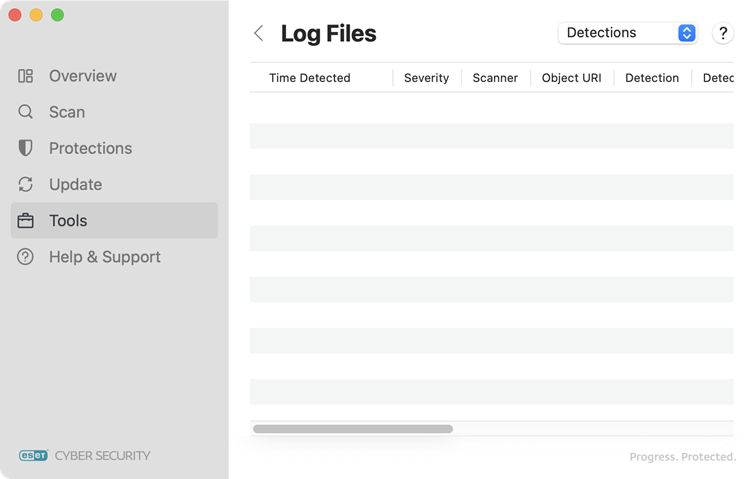
Log files are accessible from the ESET Cyber Security main menu by clicking Tools > Log files. Select the desired log type using the drop-down menu at the top right side of the window. The following logs are available:
•Detections—Displays all information about events related to the detection of infiltrations.
•Computer scan—Shows results of all completed scans are displayed in this log. Double-click any entry to view details for the respective on-demand computer scan.
•Events—Helps system administrators and users solve problems. All important actions performed by ESET Cyber Security are recorded in event logs.
•Filtered websites—Shows a list of websites that were blocked by Web access protection. In these logs you can see the time, URL, status, IP address, user and application that opened a connection to a specific website.
•Sent files—Contains records of the samples sent for analysis.